Publicly verifiable authenticated encryption
120 likes | 311 Views
Publicly verifiable authenticated encryption. Source: IEEE Electronics Letters, Vol. 39, No 19, pp. 1382- 1383, 18 th Sep. 2003 Authors: Hsiang-An, Chein-Min Lo and Tzonelih Hwang Speaker: Pen-Yi Chang, 2004/10/13. Outline. Introduction Review of MA-Chen Scheme

Publicly verifiable authenticated encryption
E N D
Presentation Transcript
Publicly verifiable authenticated encryption Source: IEEE Electronics Letters, Vol. 39, No 19, pp. 1382- 1383, 18th Sep. 2003 Authors: Hsiang-An, Chein-Min Lo and Tzonelih Hwang Speaker: Pen-Yi Chang, 2004/10/13
Outline • Introduction • Review of MA-Chen Scheme • Verification problem of the TTP in the Ma-Chen scheme • Conclusions
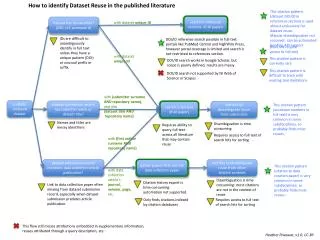
Introduction • Ma-Chen have proposed an authenticated encryption scheme with public verifiability. • Ma-Chen scheme, which the TTP can verify the sender’s signature. How- ever we will point out the verification problem of the TTP in the Ma-Chen scheme. This problem causes the TTP to reject a valid signature with non-negligible probability.
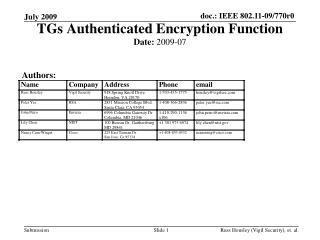
Review of MA-Chen Scheme(1/3) • Notations: p, q: large prime number with q|(p-1) g: generator of order q H: public one way hash function xa, xb: secret key of Alice and Bob ya, yb: public key of Alice and Bob m:message k: random number
Review of MA-Chen Scheme(2/3) Alice picks a random number k Alice Bob
Review of MA-Chen Scheme(3/3) For public verification: Bob computes BobTTP
Problem in TTP verification(1/5) • The reconstructed e’ by the TTP does not always equal the original e computed in the signature of the sender • Lemma 1: p, q: two prime number such that a, b: natural numbers. Let Then the probability that is
Problem in TTP verification(2/5) • Proof: Letand ,so and Let . Then • If then,
Problem in TTP verification(3/5) If then • The probability that is equivalent to the probability that • Without loss of generality, assume that is uniformly distributed in Zp .Thus, the probability that is (k+1)/p Therefore, probability that =probability that =1-(k+1)/p
Problem in TTP verification(4/5) • TTP • Alice • By Lemma 1 probability is
Problem in TTP verification(5/5) • Example Let p=23, q=11, g=2, k=10 , e (g∙yB)kmod p mod q (2∙16)10mod 23 mod 11 7 e’ (gk∙K1)mod p mod q (210∙2)mod 23 mod 11 1
Conclusions • The inequality between computing e in signing phase and public verification causes the TTP to reject a valid signature with non-negligible probability. • The TTP will reject a valid signature with probability 1 – (k+1)/p.