Network Protocols: Overview & Layering | CSC 8320 Fall 2008
Learn about network protocols, OSI model, TCP/IP suite, protocol examples, and more. Explore the syntax, semantics, and actions of protocols in communication. Understand protocol layering and the functions of each OSI layer.

Network Protocols: Overview & Layering | CSC 8320 Fall 2008
E N D
Presentation Transcript
Communication Network Protocols Jaya Kalidindi CSC 8320(fall 2008)
Overview Network Protocols OSI Protocol Suite TCP/IP Protocol Suite Protocol Examples in Internet Network References
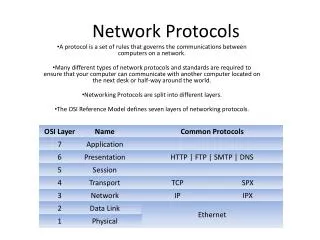
Network Protocols • Network protocols are sets of standard rules : To regulate the exchange of messages • For Representing the data,authentication and error detection. • To provide a reliable communication.
What does a protocol tell us? • Syntax of a message • what fields does it contain? • in what format? • Semantics of a message • what does a message mean? • for example, not-OK message means receiver got a corrupted file • Actions to take on receipt of a message • for example, on receiving not-OK message, retransmit the entire file
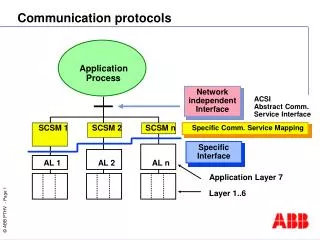
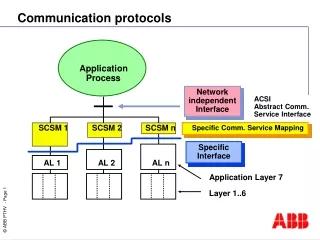
Protocol layering • A network that provides many services needs many protocols • Turns out that some services are independent but others depend on each other • Protocol A may use protocol B as a step in its execution • for example, packet transfer is one step in the execution of the example reliable file transfer protocol • This form of dependency is called layering • reliable file transfer is layered above packet transfer protocol • like a subroutine
Physical Layer • First level in Network Layer • Handles all the physical aspects of communication between two directly connected physical entities. • Provides the basis for higher level communication services. • Main functionality is to transmit bits.
Data Link Layer • This layer accepts the bit streams provided by the physical layer . • Provides reliability of transfer of data between two directly connected entities. • Its functionality includes error detection control, flow control and access control. • Divided into two sub-layers: • Medium Access Control • Logical Link Control
MAC sub-layer • Defines means by which physical means may be accessed. • It co-ordinates to seize a shared channel by multiple MAC entities. • Provides a limited form of error control. • Ethernet is an example of a shared medium with defined MAC sub-layer functionality.
LLC sub-layer • It is responsible of reliable transfer of message-link protocol data units between two directly connected layer 2 entities. • LLC services can be • Connection oriented: Frames are individually numbered and acknowledged by their sequence number. • Connection-less: Messages are not acknowledged.
Transport Layer • Concerned with getting level 4 messages form source to destination in a reliable manner. • Functions are: • Windowing and flow control. • Error detection and recovery. • Multiplexing.
Continued… • Two types of service quality: • Reliable service: makes sure that data is not lost and provides data error-free to the user. • Un-reliable service: does not have a mechanism to show that receiver has received the data sent.
Network Layer • Used to support data communication between indirectly connected entities. • Has the ability to forward messages from layer 3 entity to another, until final destination is reached. • Functions are: • Routing • Forwarding packets to final destination port. • Providing logical addressing.
Session layer • Controls communication or dialogues between applications on hosts. • Synchronization is achieved at coordinated timing . • NFS, NetBios, SQL are some examples.
Presentation Layer • Performs data transformation or formatting if required by the end applications. • Functions are: • Data compression • File formatting • Encryption • MPEG, Quicktime are some examples.
Application Layer • Provides services that directly support an application that runs on the host. • Most network management activities are based on services provided by the layer 7. • FTP, Telnet, SNMP, SMTP are some examples.
FTP (file transfer control ) Allows users to access remote file servers, list remote directories, and move files to or from remote hosts. FTP understands basic file formats and can transfer files in ASCII character or binary format., FTP provides a standard UNIX-like user interface, regardless of the actual underlying operating system.
Telnet Telnet provides a remote terminal access protocol running over Transport Control Protocol. It allows a user at one site to establish a virtual circuit connection to a remote system Using Telnet, a user at one host can login to another host, appearing like directly attached.
SNMP • Is an application service that has evolved with the growth of TCP/IP. It was derived from a low-overhead protocol designed to monitor Internet routers
UDP • The User Datagram Protocol (UDP) is a Transport Layer protocol in the TCP/IP protocol suite. UDP provides a connectionless, best effort delivery service UDP.
SMTP Email is the most widely used application on the Internet (although it does not account for the highest volume of traffic). The Simple mail transfer protocol (SMTP) provides a simple, text-oriented protocol to transfer mail reliably between TCP/IP-based systems
Reference • R. Chow and T. Johnson.Distributed Operating Systems & Algorithms. 1997 • Jim Kurose, Keith Ross, Computer Networking: A Top Down Approach Featuring the Internet, 3rd edition. Addison-Wesley, July 2004. • Cisco Systems, OSI Network Protocols, October 2006. • Diagrams:www.wikipedia.org,www. google.com